Azure Automation Role based Access Control (RBAC)
Since December 24th, Azure Automation supports RBAC. We really asked Microsoft to implement this enhancement, as lots of sensitive information and code may live within an Azure Automation account. Assets are used to store credentials, variables, connection objects. As you might have more and more contributors to the system, you probably don’t want to share all your credential objects to anyone writing automation runbooks. Before RBAC, the only way was to create multiple Automation accounts, but of course this introduced other difficulties.
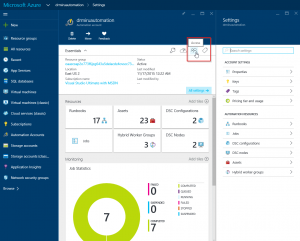
Now, here’s where you access the RBAC component.
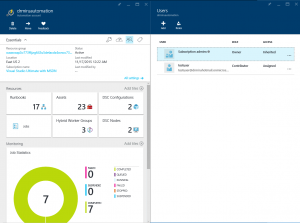
We have 5 different roles, to which we can assign users.
| Role | Permissions | ||||
| Runbooks | Resources | Roles / Access | |||
| Owner | Edit | Edit | Edit | ||
| Contributor | Edit | Use within Runbooks | — | ||
| Reader | Read | Read | Read | ||
| Automation Operator | start / stop /suspend / resume | — | — | ||
| User Access Administrator | — | — | Edit | ||
Key component behind the scenes is of course ARM (Azure Resource Manager).
Although you can’t define different access levels on single objects, you have the possibility to delegate Asset-Management to a security department, while still be able to have more Runbook authors contributing to your automation solutions.